
In today’s interconnected digital landscape, the security of our applications has become paramount. With the ever-increasing sophistication of cyberattacks, organizations must adopt a proactive approach to protect their sensitive data and maintain their reputation. This is where application security posture management comes into play.
Definition of Application Security Posture Management

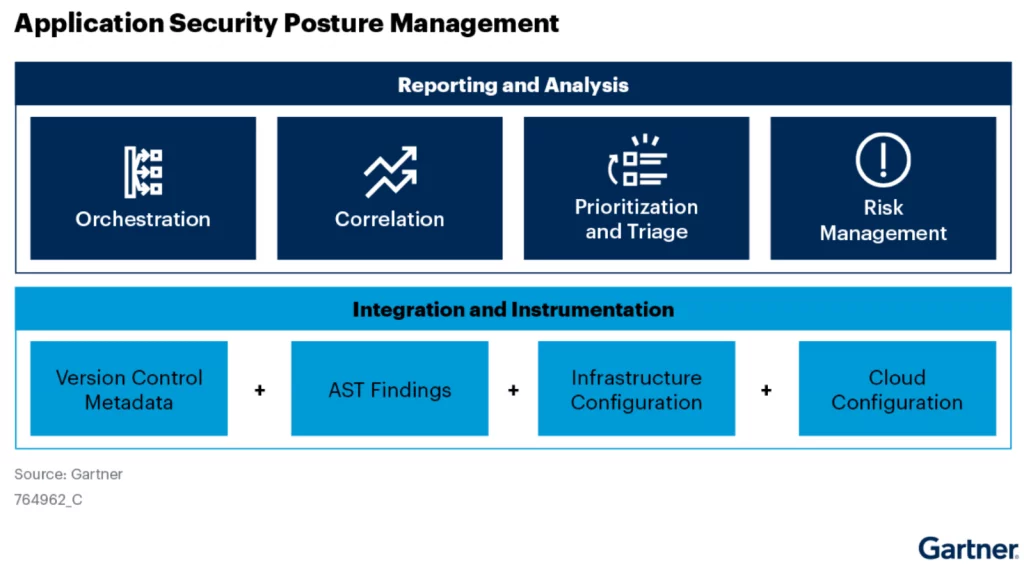
Application security posture management refers to the process of maintaining and enhancing the overall security stance of your applications. It involves assessing, identifying, and mitigating vulnerabilities and threats to ensure the robustness of your application’s security infrastructure. By implementing a comprehensive security posture management strategy, organizations can effectively safeguard their digital fortresses against potential breaches.
The Importance of Maintaining a Strong Security Posture for Applications
As technology continues to advance, so do the methods employed by malicious actors to exploit vulnerabilities in applications. A weak security posture can leave your organization susceptible to data breaches, unauthorized access, and financial loss. By proactively managing your application’s security posture, you can reduce the risk of falling victim to cyber threats and protect your valuable assets.
Overview of the Article’s Purpose and Main Points
This article aims to provide you with a comprehensive understanding of application security posture management and its significance in today’s digital landscape. We will delve into the core components of an effective security posture, explore the benefits of adopting a proactive approach, and outline best practices for managing your application’s security stance. Additionally, we will discuss the tools and technologies available to streamline the process, helping you make informed decisions to fortify your applications against potential threats.
So, buckle up and join me on this journey to fortify your digital fortresses with robust application security posture management practices. Together, we will explore the key aspects, benefits, and strategies that will empower you to safeguard your applications from the ever-evolving threat landscape.
Understanding Application Security Posture
In order to effectively manage the security of your applications, it is crucial to have a clear understanding of what application security posture entails. Let’s dive into the key aspects of this concept.
Explanation of What Application Security Posture Entails
Application security posture refers to the overall security stance of an application. It encompasses various factors, including the measures in place to protect the application, the vulnerabilities it may possess, and the level of readiness to respond to potential threats. In essence, it represents the strength and resilience of your application’s security infrastructure.
Key Components of a Strong Security Posture
To establish a strong security posture for your applications, several key components need to be considered:
1. Robust Authentication and Access Controls: Implementing strong authentication mechanisms, such as multi-factor authentication, and enforcing strict access controls ensure that only authorized individuals can access sensitive data and functionalities within the application.
2. Secure Coding Practices: Adhering to secure coding practices during the application development phase helps minimize the introduction of vulnerabilities. This includes input validation, output encoding, and secure error handling.
3. Regular Patching and Updates: Keeping the application up to date with the latest patches and updates is essential to address any known vulnerabilities and protect against emerging threats.
4. Secure Configuration Management: Properly configuring the application and its underlying infrastructure is crucial. This involves securing network connections, disabling unnecessary services, and applying secure configurations to servers and databases.
Common Vulnerabilities and Threats that can Affect Application Security
Understanding the common vulnerabilities and threats that can impact application security is vital for mitigating risks. Some prevalent ones include:
1. Cross-Site Scripting (XSS): XSS attacks involve injecting malicious scripts into web pages, potentially compromising the integrity and confidentiality of user data.
2. SQL Injection: SQL injection attacks exploit vulnerabilities in the application’s database layer, allowing attackers to manipulate or extract sensitive data.
3. Cross-Site Request Forgery (CSRF): CSRF attacks trick users into performing unwanted actions on authenticated websites, potentially leading to unauthorized transactions or data manipulation.
4. Server-Side Request Forgery (SSRF): SSRF attacks exploit the application’s ability to make requests to other servers, potentially leading to unauthorized access to internal systems or sensitive data.
By understanding these vulnerabilities and threats, you can implement appropriate security measures to mitigate risks and bolster your application’s security posture.
Now that we have a solid foundation in understanding application security posture, let’s explore the benefits of effective management in the next section.
Benefits of Effective Application Security Posture Management

In an era where cyber threats loom large, the significance of effective application security posture management cannot be overstated. By diligently managing and enhancing your application’s security stance, you can reap a multitude of benefits that safeguard your digital assets and maintain your organization’s reputation.
Enhanced Protection against Cyber Attacks
A robust security posture acts as a formidable barrier against the ever-evolving landscape of cyber attacks. By implementing proactive security measures and staying abreast of emerging threats, you can significantly reduce the likelihood of successful attacks on your applications. This includes implementing strong access controls, firewalls, intrusion detection systems, and regular security updates. With an enhanced security stance, you can fortify your applications, ensuring that sensitive data remains secure and protected from unauthorized access.
Data breaches can have severe repercussions, including financial loss, damage to reputation, and loss of customer trust. Effective application security posture management significantly reduces the risk of these debilitating incidents. By identifying vulnerabilities and implementing robust security controls, you can fortify your applications against potential breaches. This includes practices such as secure coding, encryption of sensitive data, and regular vulnerability assessments. By minimizing the risk of data breaches, you protect your organization’s sensitive information and maintain the trust of your stakeholders.
Improved Compliance with Industry Regulations and Standards
Compliance with industry regulations and standards is crucial for organizations operating in various sectors. Effective application security posture management ensures that your applications meet the necessary compliance requirements. By implementing the necessary security controls and monitoring mechanisms, you demonstrate your commitment to protecting sensitive data and adhere to the guidelines set forth by regulatory bodies. This not only helps you avoid costly penalties but also ensures that you maintain the trust of your customers and partners.
In conclusion, effective application security posture management offers a host of benefits, including enhanced protection against cyber attacks, minimized risk of data breaches and unauthorized access, and improved compliance with industry regulations and standards. By prioritizing the security of your applications, you not only safeguard your organization’s valuable assets but also foster a secure digital environment for your stakeholders. Stay tuned for the next section, where we will delve into best practices for application security posture management.
Best Practices for Application Security Posture Management

Regular Vulnerability Assessments and Penetration Testing
To ensure the robustness of your application’s security posture, regular vulnerability assessments and penetration testing are crucial. These practices help identify potential weaknesses and vulnerabilities in your application’s infrastructure, allowing you to address them proactively. By conducting thorough assessments and simulated attacks, you can uncover hidden vulnerabilities and prioritize remediation efforts. This proactive approach helps minimize the risk of exploitation by malicious actors and enhances your overall security posture.
Implementation of Secure Coding Practices
Secure coding practices play a fundamental role in establishing a strong application security posture. By following industry best practices and adhering to secure coding guidelines, you can minimize the introduction of vulnerabilities during the development phase. This includes practices such as input validation, proper error handling, session management, and secure data storage. By integrating secure coding practices into your development process, you can significantly reduce the likelihood of vulnerabilities being introduced into your applications.
Continuous Monitoring and Incident Response Planning
Maintaining a strong security posture is an ongoing effort that requires continuous monitoring and incident response planning. By implementing robust monitoring tools and techniques, you can detect and respond to security incidents promptly. This includes monitoring for unusual activities, anomalous network traffic, and unauthorized access attempts. Additionally, having a well-defined incident response plan in place enables your organization to respond effectively to security incidents, minimizing the impact and potential damage caused by a breach.
By adopting these best practices, you can establish a solid foundation for managing your application’s security posture. Regular vulnerability assessments, secure coding practices, and continuous monitoring, combined with a robust incident response plan, will help fortify your applications against potential threats. Remember, maintaining a strong security posture is an ongoing commitment that requires diligence and proactive measures to stay ahead of the evolving threat landscape.
Tools and Technologies for Application Security Posture Management

Overview of Popular Tools and Technologies
When it comes to managing application security posture, numerous tools and technologies have emerged to assist organizations in fortifying their digital assets. Let’s explore some of the most popular ones:
- Vulnerability Scanners: These tools scan applications for potential vulnerabilities and provide detailed reports on the identified weaknesses. Examples include Nessus, OpenVAS, and Qualys.
- Web Application Firewalls (WAF): WAFs act as a shield between applications and potential threats, monitoring and filtering incoming traffic. They help detect and mitigate attacks like SQL injection and cross-site scripting. Leading WAF solutions include ModSecurity, Cloudflare, and Imperva.
- Security Information and Event Management (SIEM): SIEM tools collect and analyze security data from various sources, enabling organizations to detect and respond to potential security incidents in real-time. Popular SIEM solutions include Splunk, IBM QRadar, and LogRhythm.
Explanation of Features and Benefits
Each tool and technology brings its own set of features and benefits to the table. Here’s a closer look at what you can expect:
- Vulnerability Scanners: These tools help identify vulnerabilities in your applications, allowing you to prioritize and address them before they can be exploited. They provide detailed reports, often with recommendations for remediation, helping you stay one step ahead of potential threats.
- Web Application Firewalls: WAFs offer an additional layer of protection by monitoring and filtering incoming traffic. They can detect and block malicious requests, protecting your applications from common attack vectors and ensuring data integrity.
- Security Information and Event Management: SIEM tools enable you to collect and analyze security data from various sources, providing comprehensive visibility into your application’s security posture. This allows for real-time threat detection, incident response, and compliance monitoring.
Considerations for Selecting the Right Tools
When selecting tools for managing your application security posture, several factors should be taken into account:
- Scalability: Ensure that the tools you choose can handle the scale and complexity of your applications. Consider the number of applications you have, their unique requirements, and projected growth.
- Integration: Look for tools that seamlessly integrate with your existing security infrastructure, such as your firewall, intrusion detection system (IDS), or vulnerability management platform.
- Usability: Consider the user-friendliness of the tools and the level of expertise required to operate them effectively. Training and support options should also be evaluated.
By carefully considering these factors and leveraging the right tools and technologies, you can bolster your application security posture, effectively mitigating risks and safeguarding your digital assets.
Stay tuned as we venture into the final section, where we’ll wrap up our exploration of application security posture management and conclude with a call-to-action to prioritize and invest in securing your applications.
Conclusion

In conclusion, application security posture management is not just an option but a necessity in today’s digital world. As cyber threats continue to evolve and become more sophisticated, organizations must prioritize the security of their applications to protect sensitive data and maintain customer trust.
By understanding the definition and importance of application security posture management, you have gained valuable insight into the proactive approach required to mitigate vulnerabilities and threats. Maintaining a strong security posture not only enhances protection against cyber attacks but also minimizes the risk of data breaches and ensures compliance with industry regulations and standards.
Throughout this article, we have explored the benefits of effective application security posture management, including enhanced protection, reduced risk, and improved compliance. We have also discussed best practices such as regular vulnerability assessments, secure coding practices, and continuous monitoring.
To assist you in your journey towards robust application security posture management, we have highlighted various tools and technologies available. These resources can aid in vulnerability assessments, incident response planning, and monitoring of your application’s security stance. Remember to carefully consider your organization’s specific needs and requirements when selecting the right tools for your environment.
In the rapidly evolving landscape of cybersecurity, it is crucial to stay vigilant and proactive. By investing in application security posture management, you can fortify your digital fortresses and protect your organization from potential threats.
